Physical surveillance is one of the oldest law enforcement investigative tools. If authorities suspect someone is engaging in illicit activities, the easiest path might be to follow them. This remains a widely used investigative tool, although most countries have placed limits on surveillance. A right to privacy in one's own home, for example, has near universal recognition, so countries place restrictions on such intrusion. The threshold on when government authorities can enter private spaces depends on the jurisdiction and may include probable cause, reasonable suspicion, reasonable and probable grounds, and it generally requires prior judicial authorization.
Some countries have permitted surreptitious electronic surveillance for many decades, others have allowed it more recently, and still others prohibit it entirely. This difference is due to the intrusive nature of electronic eavesdropping (Horn, 2002; Roderman, 2013; Stevens and Doyle, 2009; Solove, 2003). Where it is permitted, electronic surveillance can only be considered when less intrusive means have been exhausted or ineffectual, or when no reasonable alternative to obtain evidence can be offered, given the circumstances of the case.
Electronic surveillance performs a similar function to undercover operations, but allows for the collection of a broader range of evidence. It is a preferred investigative method when an organized criminal group cannot be penetrated by an outsider, or where physical infiltration or surveillance would represent an unacceptable risk to the investigation or to the safety of investigators. Given its intrusiveness, electronic surveillance is subject to strict judicial control and legal safeguards to prevent abuse and limit the invasion of privacy (UNODC, 2009).
|
Right to protection from arbitrary invasion of privacy The right to protection from arbitrary invasion of privacy is a fundamental human right (article 17 of the International Covenant on Civil and Political Rights (ICCPR)), so countries place clear restrictions on the allowable scope of electronic surveillance. |
Some key questions include the following for both physical and electronic surveillance (UNODC, 2016):
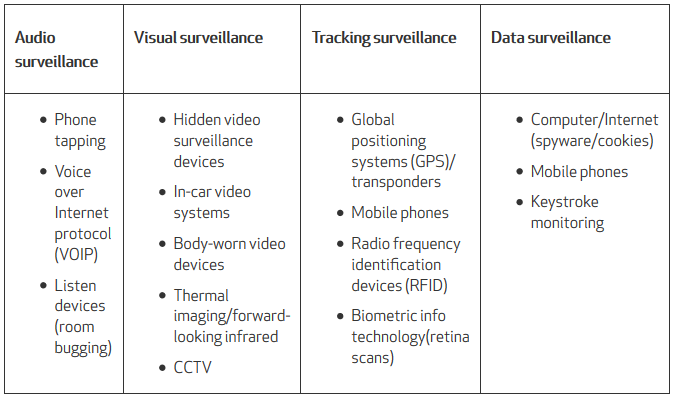
We often think of telephone tapping when considering electronic surveillance, but as Table 8.1 indicates, there are at least 15 different ways to monitor electronically a person's conversations, on-line activity, and movements. Given the dramatic growth of mobile phone usage, combined with Internet and computer surveillance methods, and public space cameras, the possibilities for electronic surveillance are daunting. Nevertheless, electronic surveillance in cases of suspected transnational organized crime has broad support, although many countries prohibit the use of electronic surveillance for less serious crimes.
Beside the limits imposed by human rights considerations, another limiting factor to more widespread use of electronic surveillance is its considerable cost. The high cost is largely due to the monitoring required of the surveillance, transcripts and analysis of what was captured, follow-up physical surveillance to confirm phone or electronic conversations, and reports requiring justification for continuing the electronic surveillance beyond an approved period (e.g., 30 days, or other domestic requirements such as production of further evidence). The increasing utilization of electronic surveillance illustrates its growing acceptance as a law enforcement tool, although issues remain about the scope of the intrusiveness of emerging technologies such as night-vision devices, thermal imagers, biometric devices, and encryption devices.