This section contains material that is meant to support lecturers and provide ideas for interactive discussions and case-based analysis of the topic under consideration.
Have students research how the largest technology companies such as Facebook, Google and Microsoft handle vulnerability reports. Ask them to answer the following:
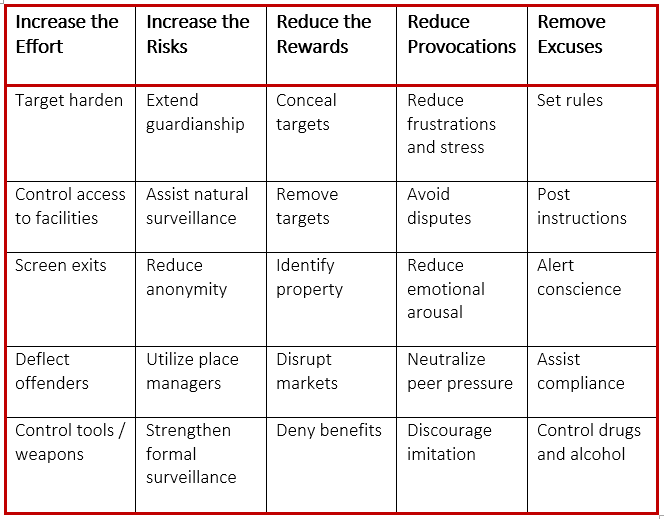
Cornish and Clarke (2003) proposed five strategies and 25 techniques (with five techniques under each strategy) to prevent and reduce crime. Assign your students to choose a cybercrime and fill out the cybersecurity techniques they would use in the below table that could be used to prevent and/or reduce that cybercrime.
In addition, students should be prepared to answer the following question:
Instruct your students to conduct research in order to identify a cybersecurity incident that involved either a private organization or public agency within the last two years. Students should come prepared to discuss their selected cybersecurity incident and the answers to the below questions in class.